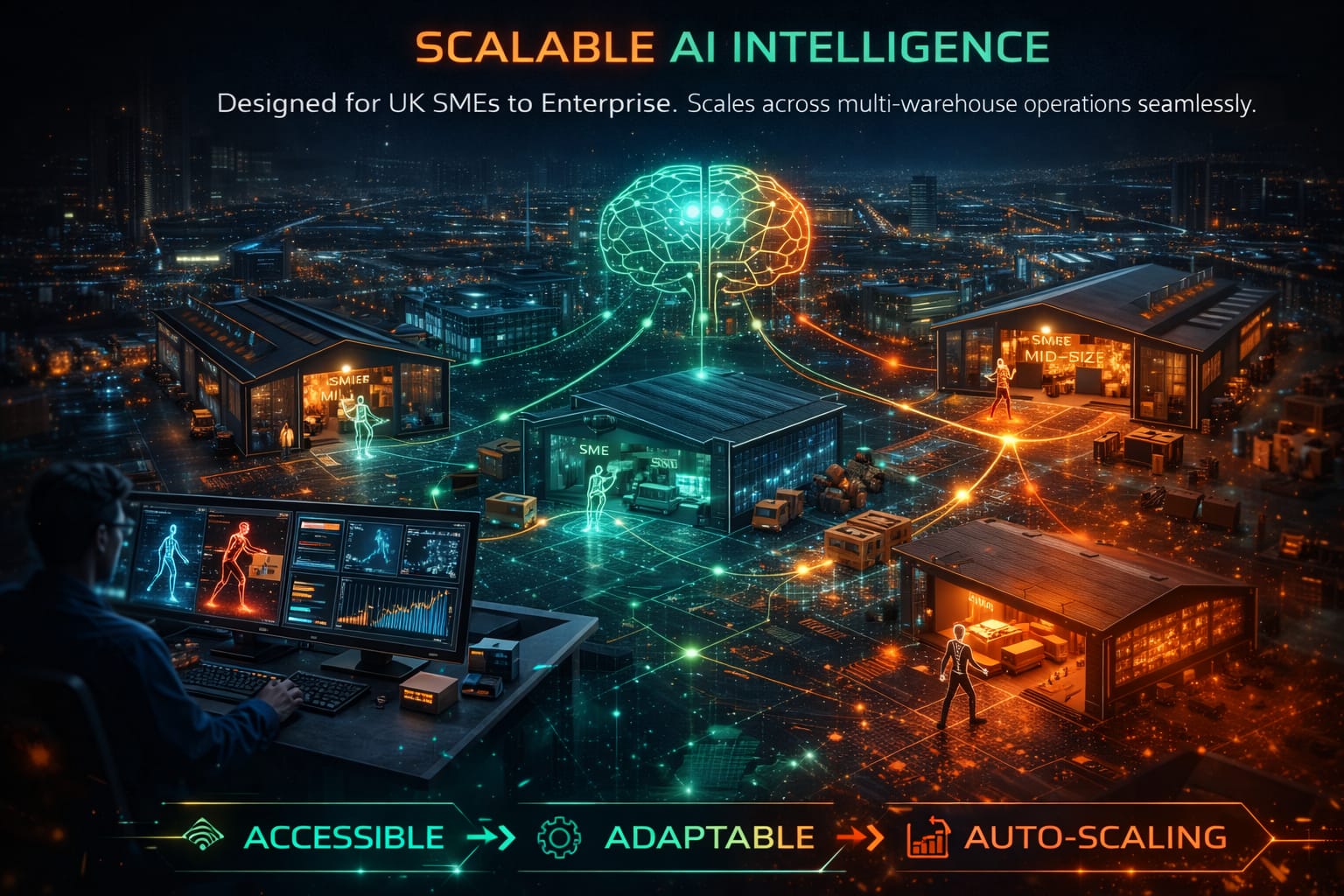
From Passive CCTV to a Real-Time Intelligent Supervisor
Generative pose estimation and contextual workflow learning convert surveillance into proactive operational intelligence.

Raw CCTV Feed
Connects to existing infrastructure. No hardware replacement.
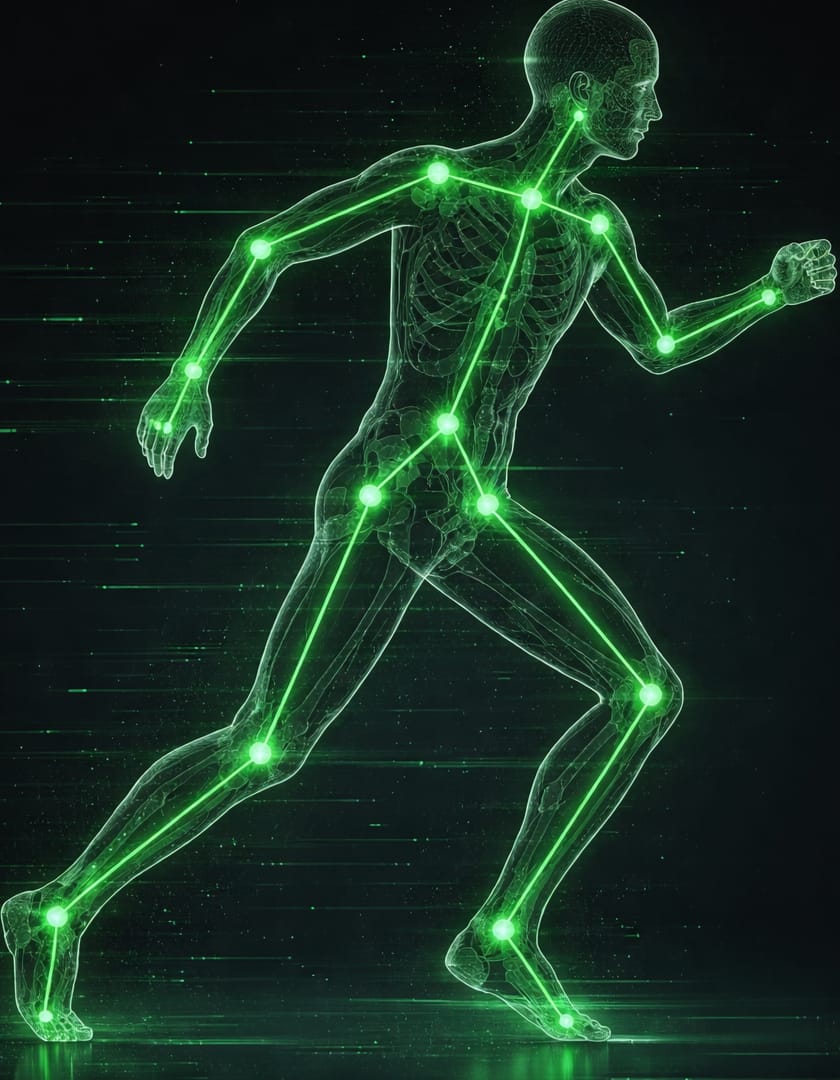
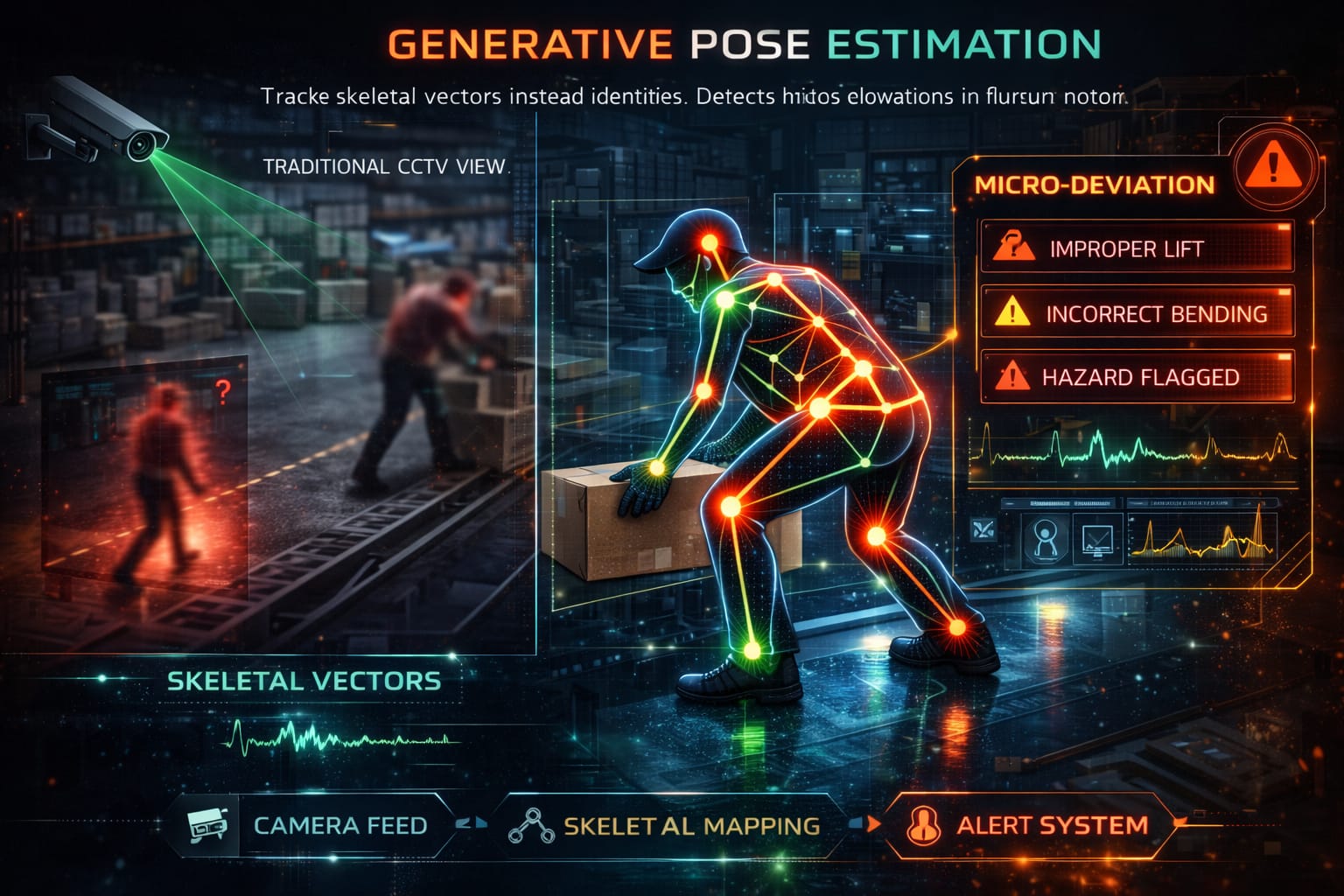
Skeletal Extraction
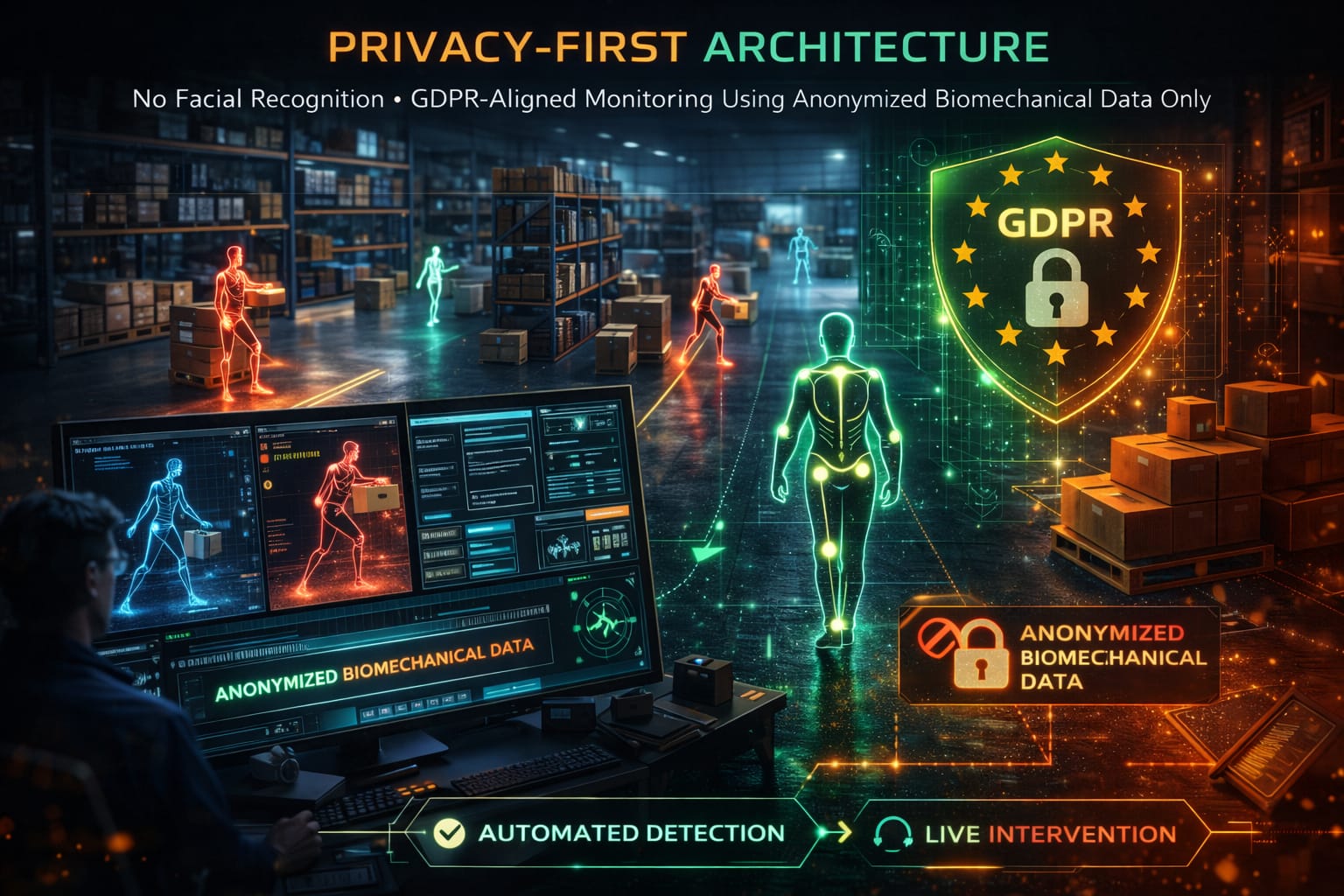
Transforms footage into anonymous biomechanical vectors.

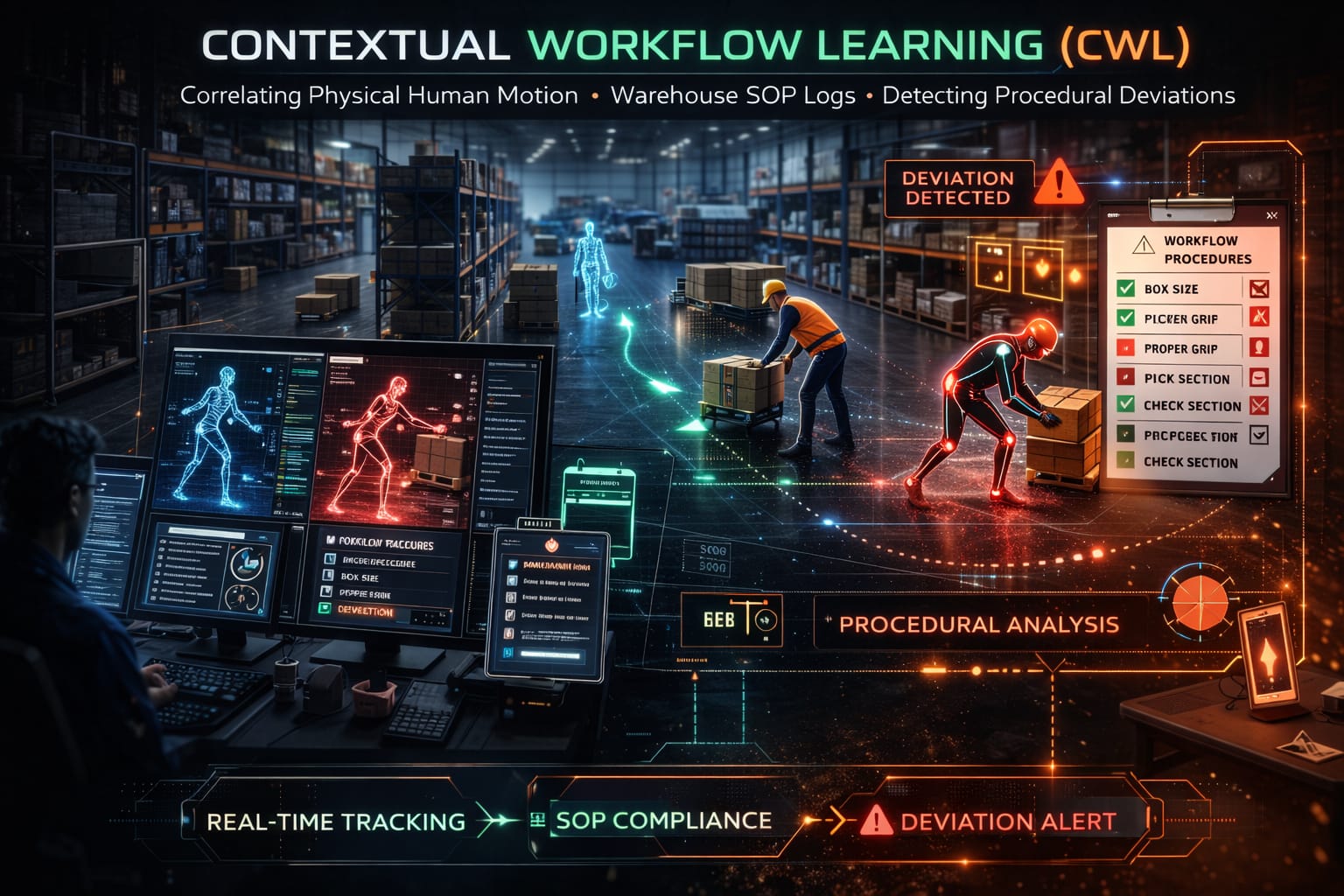
Behavior Correlation
Cross-references motion with SOP & WMS logs.

Threat Alert
Real-time intervention before loss exits facility.